Well, events 1030 and 1058 are very generic errors and can be caused by one of many different reasons. I often see questions at Experts Exchange on how to overcome these events. I don't have all the answers, but have helped out a lot of people diagnose and fix these events.
Explore Experts Exchange Articles
Our articles are written by a community of IT professionals and experts to provide insight on trending topics and common technology roadblocks.
Get AccessGet Access
Access our full library of articles written by our technology community. Read how-to guides, new perspectives on trending tech, and exclusive insights on industry news.
Articles For You
-
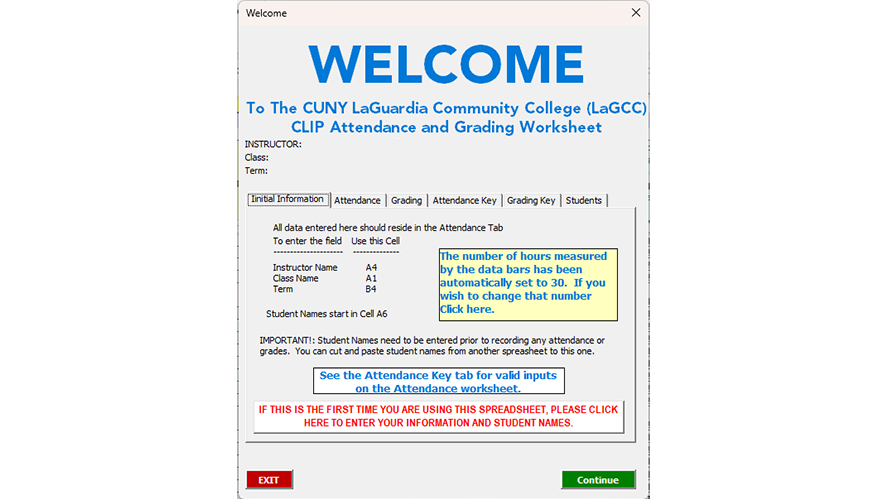
Creating a custom Welcome form in ExcelNot too long ago I wrote this article on doing the same thing in MS Access (https://www.experts-exchange.com/articles/38421/Making-your-Database-More-User-Friendly.html). I found that a similar "Welcome" screen makes Excel worksheets "friendlier" as well.
-
Resolving the MpSigStub Version VulnerabilityOften the MpSigStub vulnerability shows up in systems where an organization does not natively use Microsoft Defender for Antivirus. Therefore, other steps are needed to resolve this issue. This article shows several ways to resolve this issue.
-
How to Migrate Public Folder Contacts to Microsoft 365?In Exchange Server, we have the option to use Public Folders to store emails and other data, instead of keeping them in our mailboxes. This article tells you how to migrate public folder contacts to Microsoft 365.
-
Creating a customized Access ribbon and Network DatabaseI wrote this article because I was unable to find an article on this here on EE. Read on for step-by-step instructions on how to create a custom command ribbon in your office applications that not only make them look more professional but also protects against the ID10T error.
-
Migrate Network Policy Server (NPS) to a new serverProvides a step by step of how to migrate Windows NPS to a new server
-
Search As you Type for Microsoft Access ComboboxThis is a rather simple but effective way of searching while typing on a Microsoft Access Combobox.
-
The Best Part About Waking Up, Is Your Own Roasted Coffee In Your Cup.Most of us live by Coffee. However, are you disguising the flavor of cheap store-bought grounds (or worse, k-cups) with chemical-induced creamers? There is a much better option, and it is easier than you think!
-
ERROR_GEN_FAILURE [code 0x0000001f] When Attempting to Join vCenter to Active DirectoryIt is a common practice to join vCenter to Active Directory in order to enable AD logins and authentication to various virtual machines. However, there are times where this simple task fails. Fortunately, one of the most common reasons is due to an SMB1 issue and this describes how to resolve it.
Newest Articles
-
Improve Network Security – Separate DNS from Active DirectoryWhile deploying Active Directory with integrated DNS makes managing a domain easier, it does come with security risks. Separating out DNS can actually improve security and make things harder for a threat actor.
-
Stopping Backdoor Spam On Microsoft M365As organizations move from an on premises Exchange environment SaaS based M365. There are configurations that may allow email to slip in passed typical email filtering systems. This is all based on the configuration and described in this article, along with the solution.
-
Lessons Learned: Adding Used NVME Drive to HP ProLiant Server with ESXiInstalling used hardware in a home lab or other systems can have some challenges. Hopefully, the lesson learned here with a used NVMe drive will save someone else time and headache.
-
Exchange & Powershell is a Long HistoryA long time ago, Experts-Exchange asked me to write a little article about some Exchange interesting Powershell commands. But I was never able to finish it properly. Here is the result of this work. Exchange has been the first Microsoft product that really needed Powershell to work!
Featured Author
-
Azure Resource Locks: A Key Component of Cloud GovernanceThis article delves into the important characteristic that useful resource locks play in preserving control and making sure compliance in your Azure cloud resources.
-
What are the types of flows in Power Automate?This post provides an overview of Power Automate flow types and how to use them.
Popular Articles
-
WARNING: 5 Reasons why you should NEVER fix a computer for free.It is in our nature to love the puzzle. We are obsessed. The lot of us. We love puzzles. We love the…
-
How Do I Know What to Charge as an IT Consultant?[This article first appeared as "Why are IT services so expensive?" in my first attempt at a blog. …
-
Why you shouldn't use PST filesThey have been around for years and for thousands of Microsoft Outlook users and email …
-
Migrate Small Business Server 2003 to Exchange 2010 and Windows 2008 R2This guide is intended to provide step by step instructions on how to migrate from Small Business …
-
Outlook continually prompting for username and passwordThere have been a lot of questions recently regarding Outlook prompting for a username and password …
Join a collaborative community of technology professionals.